Fraud and Scams
INTERNET FRAUD
Learn tips for protecting your computer, the risk of peer-to-peer systems, the latest e-scams and warnings, Internet fraud schemes, and more.
To report potential e-scams, please go the Internet Crime Complaint Center and file a report. Note: The FBI does not send mass e-mails to private citizens about cyber scams, so if you received an e-mail that claims to be from the FBI Director or other top official, it is most likely a scam.
If you receive unsolicited e-mail offers or spam, you can forward the messages to the Federal Trade Commission at spam@uce.gov.
- Keep your firewall turned ON
- Install or update your antivirus software
- Install or update your AntiSpyWare technology
- Keep your operating system up to date
- Be careful what you download
CYBERSECURITY FACT SHEET
It is easy to be cybersecurity savvy with these simple tips that will go a long way to protecting you online:
Protect Your Systems:
- Use anti-virus software.
- Protect home networks with firewalls.
- Password-protect your wireless router and network.
- Disconnect from the Internet when not in use.
Protect Yourself:
- Back-up your computer regularly.
- Restrict access to your computer and accounts; sharing has risks.
- Delete emails from unknown sources.
- Use hard-to-guess passwords and keep them private.
- Don't provide personal information like Social Security Numbers, credit cards numbers, etc. with non-secure and unfamiliar web sites.
Protect Your Family:
- Help your family check computer security on a regular basis.
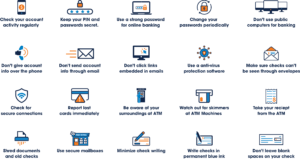
Check Fraud
What Does Check Fraud Look Like?
Check fraud can occur in a variety of ways. Some of the most common include:
- Altered Checks: Fraudsters erase and change check details using rubbing alcohol or other solutions, modifying the payee or amount before cashing it with fake ID. They may also exploit blank spaces to add unauthorized details.
- Forged Checks: Criminals steal blank checks, fill in the details, and forge the account owner’s signature.
- Counterfeit Checks: Fake checks are created using office supplies or software, then printed with stolen banking information to appear legitimate.
Consider these eight possibilities to help you avoid check fraud:
- Online Bill Pay: Enables safe payments without checks, saving time and protecting personal information.
- Money Transfer Apps: Apps like Zelle and Venmo allow quick, safe fund transfers using mobile numbers or emails, eliminating the need for sharing bank info.
- Wire Transfers: Secure for domestic and international transactions, typically faster than checks but come with fees.
- Bank-Generated Checks: Banks can send checks on your behalf, adding a layer of security to payments.
- Caution with Checks: Avoid mailing checks to reduce the risk of theft and consider digital alternatives.
- Positive Pay Services: Businesses can use services that detect check fraud by validating check issuance details against presented checks.
- High-Security Checks: Opt for checks with enhanced security features to reduce fraud risk.
- Chemically Reactive Paper: Use checks made from chemically reactive paper to indicate any alterations made by fraudsters.
Identity Theft Prevention
Identity theft is the unlawful use of another person’s identification. It can destroy the financial history you have worked so hard to obtain. The following lists ways that you can help protect yourself from identity theft.
General Identity Theft Protection
- Keep any items containing confidential information safe e.g. Social Security cards, Driver’s License number and financial information.
- Never release any personal information to anyone over the phone unless you initiated the call.
- When disposing of confidential information, please do so by shredding.
- Never respond to an email requesting personal information.
- Make sure you do business with reputable companies, especially internet based.
- Avoid storing your banking password or other sensitive information on your computer, smartphone or in an app where it could be discovered if your device is stolen.
- Review your credit report at least once a year to look for unauthorized accounts opened in your name. Receive a free credit report from each of the three major credit bureaus at www.annualcreditreport.com.
Bank Account and Card Security
- Report lost or stolen cards and checks immediately.
- Review account statements carefully. Doing so will help quickly detect and stop fraudulent activity.
- Limit the amount of information that is written on checks.
- When selecting a Personal Identification Number (PIN) don’t use any number or word that appears in your wallet (such as name, birth date, or phone number).
- Ensure no one sees your PIN when you enter it. Never share your PIN with anyone.
- Always keep your debit and credit cards in a safe and secure place.
- If you receive a replacement debit or credit card, cut up and discard your old card.
Tips for Protecting Your Child’s Personal Information
- Talk with your child about safe online practices.
- Help your child learn to analyze advertisements, some of which may be fraudulent.
- Secure electronic equipment.
- If a company wants to collect data on your child, find out why.
- Be aware of possible signs that a child is the victim of identity theft.
- Consider asking the three major nationwide credit reporting agencies—Equifax, Experian, and TransUnion—to check if your minor child has a credit report.
Reporting Identity Theft
In the event that you suspect your identity has been stolen or you are, in fact, certain that it has been stolen follow these simple steps. Report Identity Fraud & Identity Theft
Other Resources:
Identity Theft Resources Center
The National Fraud Information Center
FDIC Consumer News: A Bank Customer’s Guide to Cybersecurity